Paar märkust endale, et ei peaks koguaeg Googlit kulutama.
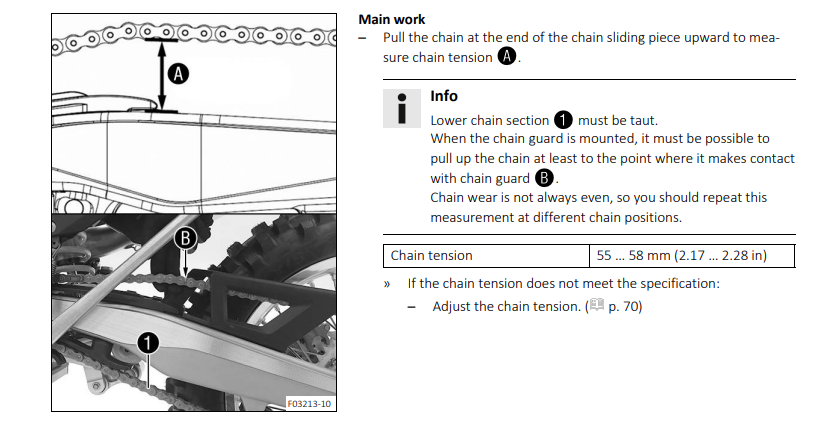
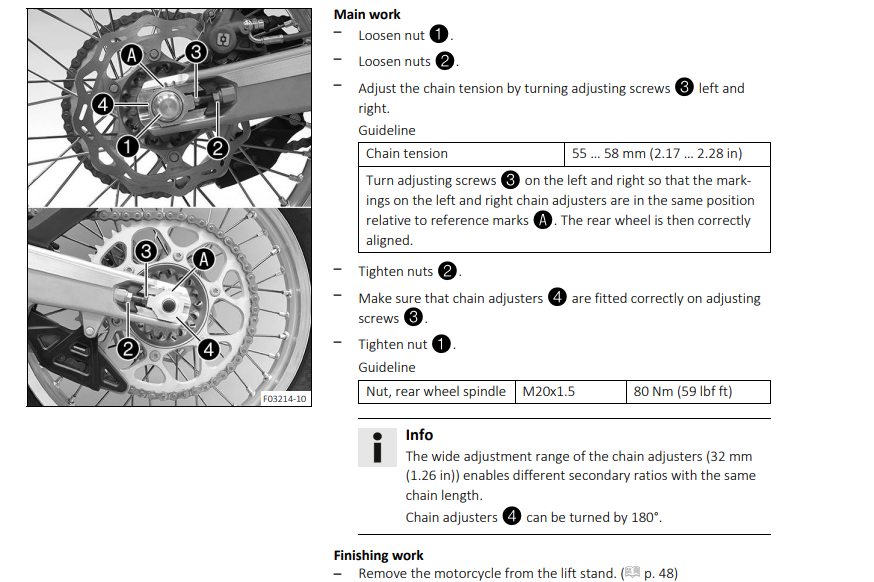
Originaal https://azwecdnepstoragewebsiteuploads.azureedge.net/21_3215013_en_OM.pdf
If you're inventing and pioneering, you have to be willing to be misunderstood for long periods of time
In case you have free space in volume group it is easy to increase logical volume.
Check volume group free space:
vgs
Extend logical volume by 1G:
lvextend -L +1G /dev/sysvg/var
Resize part:
xfs_growfs /dev/sysvg/var
Done!
§ 10. Arvestuslike kirjalike tööde hindamine
(1) Hindamisel võetakse aluseks järgmine protsendiskaala:
1) 90–100% punktide arvust – hinne «5»;
2) 70–89% punktide arvust – hinne «4»;
3) 50–69% punktide arvust – hinne «3»;
4) 25–49% punktide arvust – hinne «2»;
5) 0–24% punktide arvust – hinne «1».
Loeme flash sisu faili blink.hex:
avrdude -v -V -c arduino -p atmega328p -P /dev/cu.usbmodem1201 -U flash:r:blink.hex:i
Kirjutame failisisu blink.hex arduino flash mälusse:
avrdude -v -V -c arduino -p atmega328p -P /dev/cu.usbmodem1201 -U flash:w:blink.hex:i
Loeme eeprom sisu faili eeprom-blink.hex:
avrdude -v -V -c arduino -p atmega328p -P /dev/cu.usbmodem1201 -U eeprom:r:blink.hex:i
Kirjutame failisisu eeprom-blink.hex arduino eeprom mälusse:
avrdude -v -V -c arduino -p atmega328p -P /dev/cu.usbmodem1201 -U eeprom:w:blink.hex:i
Kompileerime hello.asm faili:
;hello.asm
; turns on an LED which is connected to PB5 (digital out 13)
.include "./m328Pdef.inc"
ldi r16,0b11111111
out DDRB,r16
out PortB,r16
Start:
rjmp Startavra hello.asm
Laadime kompileeritud hex faili hello.hex kivi peale flash mälu osasse:
avrdude -v -V -c arduino -p atmega328p -P /dev/cu.usbmodem1201 -U flash:w:hello.hex:i
docker run -e SSL_SUBJECT="example.com" paulczar/omgwtfssl
https://github.com/paulczar/omgwtfsslMa olen meeldivalt üllatunud, et 3DC.io eestlaste tehtud on.
Esimeseks katseks võtsin maja. Mida rohkem ma sellega tegeleda üritasin, seda hullemaks läks. Hea soovitus – salvesta vaheetapid.
3D printeri olemasolul koolis ilmselt tormaks paljud kohe printima, mis on iseenesest hea. Mõne aja pärast ilmselt õpiksime, et kõike ei saagi printida ja seeläbi saaksime sammu tagasi astuda ja mõelda, miks ei saa.
Seda, mida printida võiks arutelu käigus selguda. Selleks ajaks on ehk esimesed katsetused ka tehtud ja aru saadud, mida on mõtet ja mida mitte printida.
Leidsin ja nüüd panen siia enda tarbeks ühe lingi, kus väga mõistlikult (minu jaoks) selgitatakse sin, cos ja tan lahti.
Juhtusin biker.ee foorumis lugema arutelu mootori võimsuse üle ja Randeli seletus meeldis niivõrd, et peab endale kohe ülesse kirjutama. Tsitaadi algus:
Et maakeeles võimsuse ja pöördemomendi vahe selgeks teha, kujutlege järgmist olukorda:
On vaja tassida 100 tellist punktist A punkti B
Üks tööline tassib 10 kivi korraga (suur pöördemoment) ja teine 2 kivi korraga (väike pöördemoment)
Esimene tööline käib aeglaselt (madalad pöörded) ja teeb töö ära näiteks 1 tunniga.
Teine lidub kiirelt (kõrged pöörded) ja saab 45 minutiga hakkama.
See kumb saab töö kiiremini tehtud, ongi võimsam.
Mootoriga on täpselt sama loogika.
Tsitaadi lõpp.